This week the following subjects caught my attention:
1. CRTO
I was feeling pretty upset with myself over the fact that I had purchased a subscription to ZeroPointSecurity’s Certified Red Team Operator (CRTO) course and hadn’t really dedicated any time to working through it. However, much to my surprise, the course’s creator and moderator - RastaMouse (who has contributed in many ways to the InfoSec community a la HacktheBox’s RastaLabs) - announced that the lab was migrating to a new SnapLabs environment. As a consequence, I could petition to migrate my subscription over to the new lab format; now my hours in the lab only decrement when I spin up the lab machines (a la AWS pay-what-you-use billing).
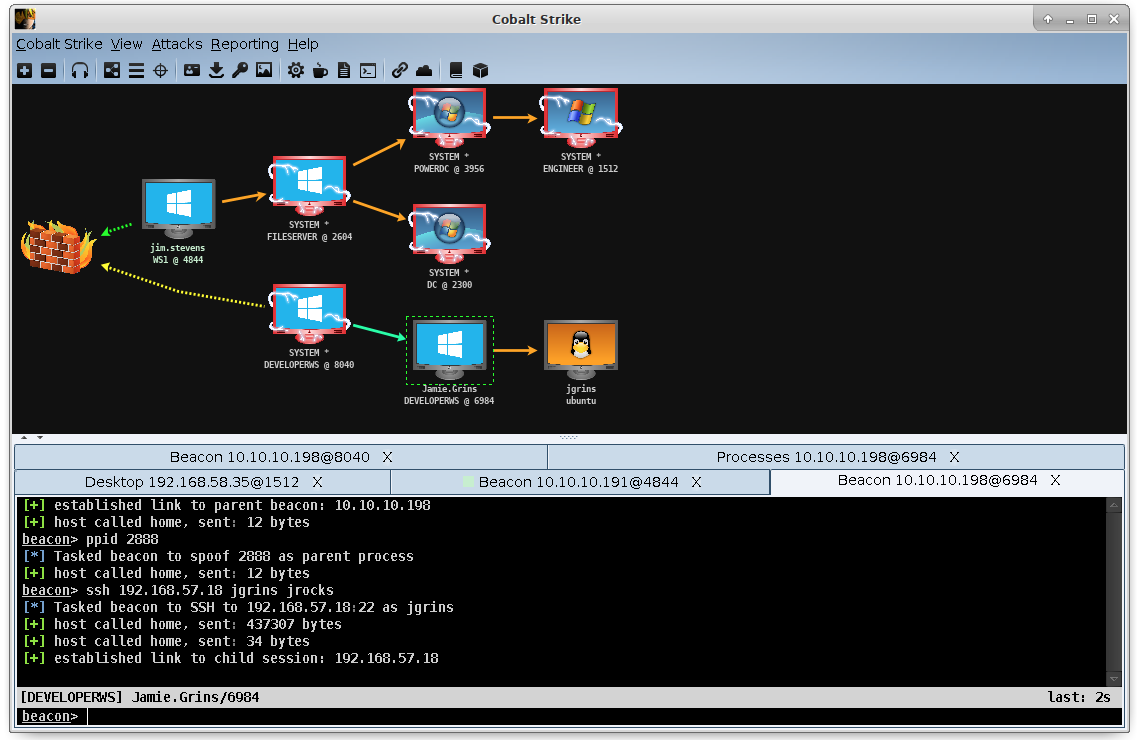
Moreover, yet another plus was that the labs hosted on AWS include a working subscription to Cobalt Strike; this was an attack tool suite my employer indicated they wanted us to use in the future, so this synergy in training was quite convenient.
I really have to applaud this migration and course delivery re-vamp; the quality of the content is top-notch.
2. Rubber Duckies
I had the opportunity at work recently to explore using a hak5 rubber ducky.
In brief, a rubber ducky leverages the badUSB vulnerability, which - in a nutshell - has a pre-programmed usb device act as a Human Interface Device (HID), like a keyboard or mouse. Thus, when an unsuspecting victim plugs such a device into their machine (mistaking it for a legitimate/innocent usb device), the rubber ducky submits a series of pre-programmed commands to the machine as though the user were entering in the keystrokes/clicks themselves.
There are folks a whole lot smarter than me who have gone to great lengths to explore the potential of this attack (such as making a wifi-enabled version or ones that look and work like charging cables); however, I was really tickled in having the opportunity to lay hands on the device myself and work through programming it. Ultimately, the attack I programmed it to do was harmless: I just had it run a batch file that threw out random red-colored numbers (a la “The Matrix”). Moreover, I became really interested in seeing if I could engineer my own badUSBs at a lesser cost (more on this later, if it works).
3. Hacking Demonstrations
I was tasked recently with drumming up some demonstrations for a non-technical audience to help serve as learning aids for InfoSec training.
This turned out to be a really fun exercise, and I was pretty pleased with how they turned out (especially given the short turn-around time they needed to be delivered in). One was the rubber ducky exercise (mentioned above) and the other involved a logic bomb scripted into Windows’ scheduled tasks (ultimately leading to a remote takeover of the victim’s webcam).
I also pitched (but ultimately had shelved) working through this really neat Industrial Control Systems (ICS) attack setup that can be hosted entirely in a virtualized environment. The GRFICSv2 set of VMs even comes with a set of training videos demonstrating an attack (or series of attacks) that can be performed.

While I always want to make sure that I’m improving my own technical aptitude, it was really neat to be able to create this training for others.
4. Synack
After a looooooong stretch of back-and-forth, interviews, and background checks, I’ve finally been accepted into Synack’s Red Team (SRT).
I’ve been excited to be a part of this group; frankly, I’m nervous about getting into bug bounties at all, but Synack has a lot of positive reviews. Moreover, my former co-worker likewise favorably described the organization. I’m looking forward to engaging with them. If nothing else, this should be a great opportunity for me to continue developing my professional skills.
5. A Little Much on the Plate
I’ve been feeling a little stretch thin this month: an unfortunate series of events occurred at work that has put some added workload on my plate, my grad school course is approaching midterms, I haven’t been able to devote as much time as I’d like to the CRTO, I’m not getting as much exercise as I want, and I want to devote more time to my family.
As much as I’d love to dive head-long into the infinite ocean of learning material that exists out there in InfoSec (and software development in general), I think I need to pare down some of my responsibilities and implement some better scheduling of my time. I’m not sure yet what that will look like; but I’m afraid that if I don’t deliberately set aside some recurring me-time, I’ll begin dropping things all around.
