Preamble
Hack the Box (HTB) offers an array of challenges irrespective of the Active/Retired machine list. One such challenge is “Emdee five for Life” which presents an interesting one-off web problem.
On initially starting the target, the attacker is presented with an IPv4 address and port which we can navigate to in a web browser:
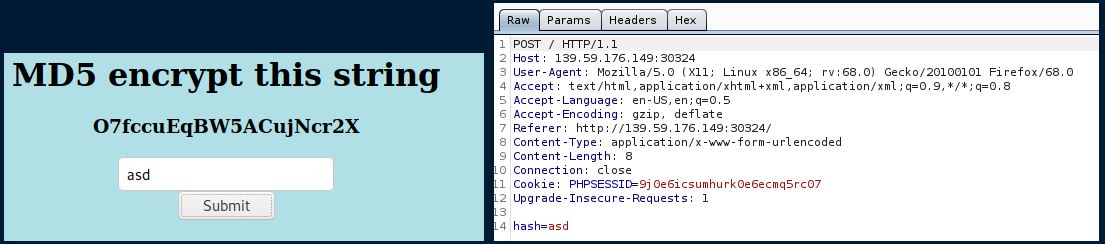
In the image above, the left snapshot is what we see in the browser and the right is what is visible within the request when we click “Submit”.
When the page renders however, we see that the response redirects us back to the same page, only this time with an added message of “Too Slow!”. Note: I did attempt at this point to take the string given, encrypt it with md5, then submit it in the hash field in the request above - but this too proved to be too slow.
If speed is needed, then the only solution would be to write a script to handle the problem.
I began by crafting a bash script, since I knew an easy way to make GET/POST requests was by invoking the curl command. I had the added benefit of getting some practice with bash scripting as well. The final script is below:
#!/bin/bash
url=http://46.101.84.35:31562
html=$(curl -c cookie ${url})
echo $html
echo
code=$(echo -n $html | awk -F "<h3 align='center'>" '{print $2}' | cut -d "<" -f 1 | sort | uniq -u)
echo "The code is: " $code
encrypted=$(echo -n $code | md5sum | cut -d ' ' -f 1)
entry=hash=$encrypted
echo "The entry is: " $entry
echo
curl -b cookie -X POST -F $entry $url
So what’s happening in this script?
The first line denotes the Shebang header of the bash script. It specifies that the rest of the code should be interpreted with /bin/bash.
Line 3 sets the url variable to the target, which is used in other commands elsewhere within the code.
Line 5 executes a curl command to the url, which by default is a GET request. The -c cookie option also saves the cookie from the request to a file named “cookie”; this cookie information is necessary later. The output of the curl request is saved to variable html. For reference, the output looks like:
<html>
<head>
<title>emdee five for life</title>
</head>
<body style="background-color:powderblue;">
<h1 align='center'>MD5 encrypt this string</h1><h3 align='center'>ZHPImAi899i1cYQD2WlY</h3><center><form action="" method="post">
<input type="text" name="hash" placeholder="MD5" align='center'></input>
</br>
<input type="submit" value="Submit"></input>
</form></center>
</body>
</html>
Line 9 performs some filtering on the text saved to html. Our goal from the filtering is to isolate the string that needs to be encrypted, which we note is between the only h3 tags in the page HTML. Therefore, we first pipe the output through awk, which allows us to split each line by a particular field marker (in our case, the first h3 tag), specifying the option {print $2} in order to pull all of the contents after the h3 tag. This returns the following:
ZHPImAi899i1cYQD2WlY</h3><center><form action="" method="post">
Line 9 then pipes this output through the cut in order to remove all the content after the “<” character, with the option -f 1 specifying we want to keep everything before it. Finally, it’s piped twice more through the sort and uniq commands in order to do away with the newline drops before and after the string. The final string output is saved to the bash variable code.
Line 12 performs the MD5 encryption by piping the string (sans “\n”, hence the -n option in echo) to md5sum. Note: the md5sum command provides the encrypted output with a trailing “ - ” character, so we pipe this yet again through the cut command.
Line 13 saves the encrypted string in the format necessary for the POST request.
Finally, Line 17 performs the POST request with curl; we include the formatted hash field with the -F option; we also include the cookie saved back in line 5. If we did not, we would be essentially passing the encrypted string to an entirely different request (ergo, mismatched string to encrypted-string).
This yields the following output:
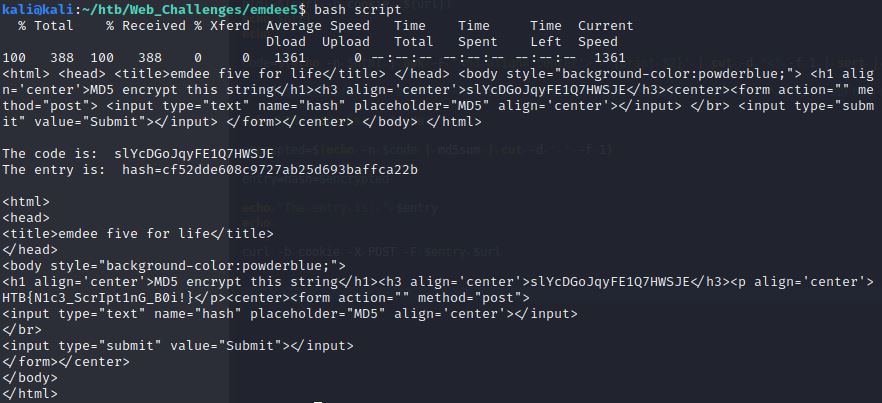
Reading the final HTML output reveals the desired flag: HTB{N1c3_ScrIpt1nG_B0i!}