In the wake of the Coronavirus Disease 2019 (COVID-19) that has impacted people worldwide, a multitude of new cyber threats have been arisen.
Zoom
As a result of “stay at home” orders issued by governors across the United States, many people have had to adapt in interacting with their peers and coworkers from home. One prominent technology that is being widely adopted is Zoom, a video conferencing application developed by the American communications technology company Zoom Video Communications, Inc. Zoom’s use has seen a meteoric rise in the last several weeks among employees looking to work remotely, students engaging their lesson plans at a distance, and many others looking for a convenient and popular means of video conferencing with one another. However, in that same time there have been a number of security vulnerabilities publicly disclosed by security researchers.
According to Bruce Schneier, “Zoom’s problems fall into three broad buckets: (1) bad privacy practices, (2) bad security practices, and (3) bad user configurations.”. That is to say, Zoom’s problems are:
- Zoom’s privacy policy permits the collection and exchange of personal information about its users for payment. This information includes (but is not limited to): your name, physical address, email address, phone number, job information, social media, host machine information, IP address, and more. This is an extensive amount of information that is arguably unnecessary for a video conferencing application.
- An array of security vulnerabilities have been reported by various researchers, including one that permitted attacker’s to enable a user’s camera without permission, another that enabled attackers to steal users’ Windows credentials , and a third that permitted attackers to spy on meetings that they weren’t approved to attend – thereby listening to potentially privileged information .
- Zoom has struggled to keep pace with patching these vulnerabilities and – as a result – the product has been repeatedly exploited by online trolls in a practice known as “Zoombombing”. Subsequently, Taiwan, Australia, and New York City have all either limited the product’s official use or banned it outright.
“Skilled threat actors are exploiting peoples’ concerns about Coronavirus to spread mobile malware, including Mobile Remote Access Trojans (MRATs), Banker Trojans, and Premium Dialers, via apps which claim to offer Coronavirus-related information and help for users.”
Spyware
Many people are concerned about tracking the presence (or absence) of COVID-19 cases near them. To this end, a number of cyberespionage applications are being discovered masked as information services regarding the epidemic. These include:
- Mirrored copies of the Johns Hopkins coronavirus tracker of infection rates and deaths that contain a customized version of SpyMax.
- A mobile app that steals social media messages, texts, contact lists, call logs, photos, location, and device information misleadingly advertised as “Coronavirus Updates”.
- Israeli surveillance software pitched as a means to better understand how COVID-19 is spreading.
Check Point Research has reported 16 different mobile apps which claimed to serve as information resources regarding COVID-19 but instead contain malware. The researchers reported that, “Skilled threat actors are exploiting peoples’ concerns about Coronavirus to spread mobile malware, including Mobile Remote Access Trojans (MRATs), Banker Trojans, and Premium Dialers, via apps which claim to offer Coronavirus-related information and help for users.”
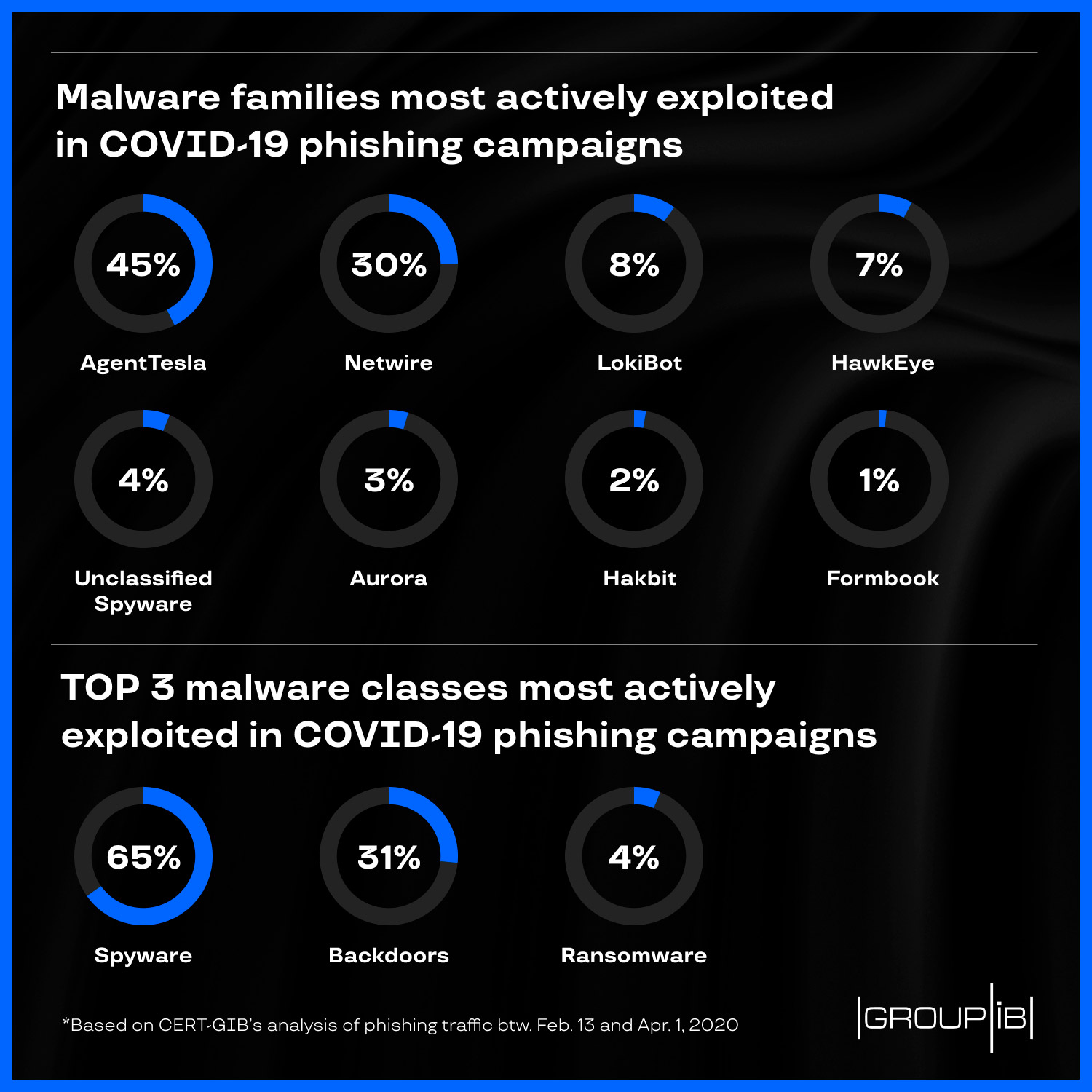
Phishing Schemes
In the absence of centralized federal guidance, the individual state governors have been issuing a series of their own advisories for their respective populaces. As such, attackers have been launching phishing campaigns masquerading themselves as those advisory notices, purchase orders, face mask offers, and alerts/safety recommendations from organizations such as the World Health Organization (WHO), UNICEF, and other such agencies.
While most of these phishing attempts have come in the form of emails, the National Cyber Security Centre (NCSC) also reported attempts by other means (ex: text messages). According to their report, these SMS messages – with signatures such as “COVID” and UKGOV” – allude to government payments and tax rebates (such as the trillion dollar bailout passed by U.S. Congress last week) and include links directly to the phishing site.
The FBI has issued a reminder that U.S. government agencies are not sending unsolicited emails or texts asking for private information in order to send stimulus checks. The Internal Revenue Service (IRS) will distribute payments to most Americans via direct deposit information that the agency has on file from previous tax filings.