Kevin Mitnick’s “Ghost in the Wires” is an autobiography providing insight into the prolific hacker’s rise, fall, and misadventures all around. The book, published originally in 2011, provides anecdotal accounts both of Mitnick’s technical prowess and – more impressively – his social engineering aptitude.
This latter skill is what is truly amazing: Mitnick’s ability to exploit social norms and manipulate people is staggering. “People, as I had learned at a very young age, are just too trusting,” Mitnick says. His insights in human behavior have proven invaluable in both the private and government sector:
- On preparation – “The basic tactic is simple. Before you start social engineering for some particular goal, you do your reconnaissance. You piece together information about the company, including how that department or business unit operates, what its function is, what information the employees have access to, the standard procedure for making requests, whom they routinely get requests from, under what conditions they release the desired information, and the lingo and terminology used in the company.”
- On susceptibility – “When you know the lingo and terminology, it establishes credibility – you’re legit, a coworker slogging in the trenches just like your targets, and they almost never question your authority. Why was the lady in Line Assignment so willing to answer all my questions? Simply because I gave her one right answer and asked the right questions, using the right lingo. So don’t go thinking that the Pacific Bell clerk who gave me Eric’s address was foolish or slow-witted. People in offices ordinarily give others the benefit of the doubt when the request appears to be authentic.”
- On fear – “I got into the U.S. Leasing’s system using a tactic that was so ridiculously easy I should have been embarrassed to try it…I would call the company I’d targeted, ask for their computer room, make sure I was talking to a system administrator and tell him…’We’ve discovered a catastrophic bug…You could lose data.’ This is a very powerful social-engineering technique, because the fear of losing data is so great that most people won’t hesitate to cooperate.”
- On foreign targets – “…a telephone receptionist found someone who spoke English to translate for me. That’s always an advantage, because the translator lends authenticity: she’s right there in the same building, speaking the same language as your target. The person at the end of the chain tends to assume you’ve already been vetted.”
People, as I had learned at a very young age, are just too trusting.
While many of the technologies Mitnick hacked in his youth may be deprecated now, people are still just fallible (if not more so for the level of trust passed onto present technical security solutions). Readers interested in a more in-depth explanation of his techniques may be interested in picking up his 2002 publication, “The Art of Deception”.
To be sure, Mitnick is not only clever but technically apt as well. His knowledge over telecommunications systems is unparalleled, manifesting itself in so many ways in his hacking efforts (colloquially referred to as “phone phreaking”). This, coupled with his social-engineering talents, is what made Mitnick such a capable hacker.
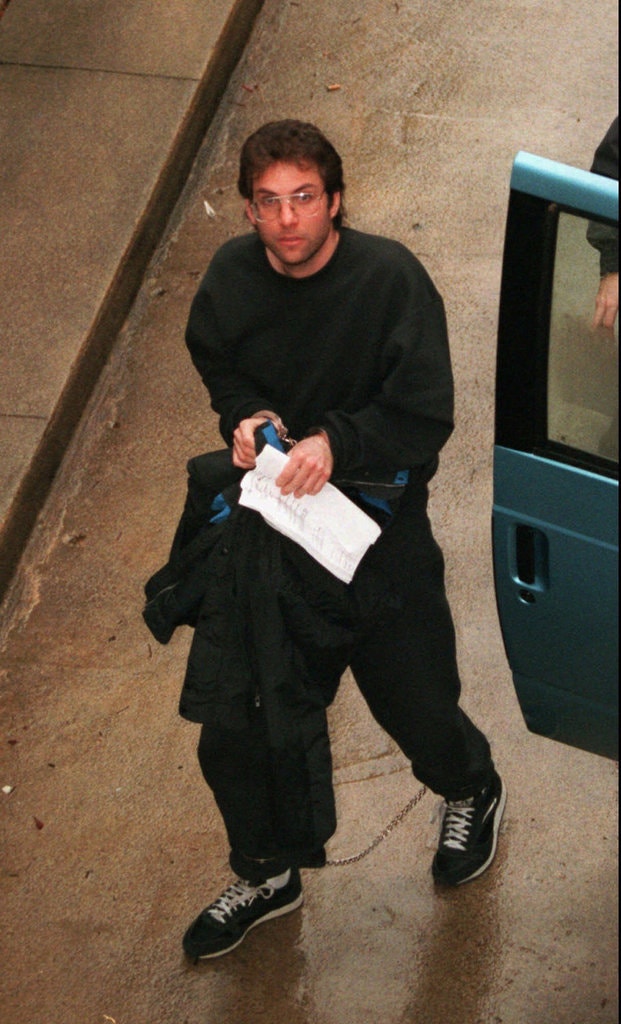
Prior to its publication, Mitnick’s reputation was – and in some circles, remains – controversial due to his very public manhunt, trial, and sentencing along with adaptations of these events in the 2000 film “TakeDown”. It’s clear Mitnick takes issues with how he was treated by the U.S. criminal justice system as well as the film’s consultants, Tsutomu Shimomura and John Markoff. He rhetorically asks how his court-appointed attorney could be so incompetent in defending Mitnick; he balks at charges leveled at him, attributing their claims to “…tall tales, likely picked up from bogus media reports…”; and he bemoans how he is portrayed in the aforementioned film.
The screenwriters had cast me as an evil villain and portrayed me as doing things I had never done in real life, such as hacking into hospitals and endangering patients’ lives by altering their medical records. I was horrified.
It’s clear – at least in Mitnick’s retelling – that his opposition pulled very few punches in his early life: friends/accomplices turned on him, prison systems – not knowing what to do with the advent of cyber criminals, like Mitnick – dumped him into solitary confinement, and prosecutors seemed eager to play-up Mitnick’s charges to judges who lacked the technical knowledge to understand the extent of his criminal behavior. However, it’s also clear that Mitnick doesn’t spend time on introspection over many of his actions that got him in these places, including (but not limited to):
- Manipulating phone company switches all across America
- Getting information from the DMV in an unauthorized capacity
- Tapping into an FBI informant’s phone call
- Listening to voicemail messages of Pacific Bell Security agents
- Illicitly obtaining and using proprietary source code from several companies, including Nokia
Over the previous four years, I’d had to deal with libelous reporters, uncomprehending judges, superstitious Marshals, manipulative friends, and exploitative filmmakers fanning the flames of the Myth of Kevin Mitnick for their own agendas.
Aside from his immediate family – who he repeatedly subjected to duress in covering his escape antics, including abandoning his Grandmother for hours outside a Kinko’s while he fled police – Mitnick doesn’t seem to really see his actions as having wronged anyone. He jokes about threatening a woman who turned evidence – purportedly false – over to investigators. He disparages his ex-wife, whom he married in order to avoid having her turn state’s witness against him, and then hacked her phone to eavesdrop on when she announced she was filing for divorce. When fired from GTE’s IT department after 9 days for failing to disclose that he had hacked their systems for years, he floats the notion that he might never have hacked again if he had only been allowed to work there; he says this, despite numerous instances throughout the book where he claimed he had “given up hacking for good” or held IT positions with other firms.
To these points, Mitnick purports he was driven to hack not by malicious or criminal motives, but by a compulsive disorder. He stylizes his life as being “like a character in a bad spy movie” or “like a character in a spy novel”. Not even at the books end, with his prison sentence behind him, does he ever stop to reflect that there ever were any alternative choices he could have made; instead, he highlights his successes as a businessman, talk-show guest, and cyber consultant. It is his autobiography, after all.
Ethical hacking (“White Hat Hacking”) does not necessitate a criminal background to enter the field. While there are many individuals that have a wide range of personal histories that make up the profession, its perfectly acceptable to pursue an education in the topic without committing the multiple state- and federal-level crimes that Mitnick has. Mitnick is extraordinarily lucky to have the life he has now, given his history. That much, he acknowledges.
For more on the life and misadventures of Kevin Mitnick, pick up his autobiographical account “Ghost in the Wires,” available now.