The RiceTeaCatPanda (RTCP) Capture-the-Flag (CTF) 2020 competition was a jeopardy-style cyberskills event that challenged competitors to solve problemsets that included topics such as cryptography, web, binary, forensics, general computer skills, data analysis, AI hacking, and more.
While the competition was slated to take place over the course of 5 days, I participated only in the final hours of the competition due to work constraints. This was unfortunate: in retrospect, I wish I had spent the full amount of time working on the problems, since this was a CTF that I felt fairly competent and engaged with!
In the span of just over 4 hours, I solved (6) of the challenges for 356 points. While this was a far cry from the overall winning team in the competition (30,581 points), I was pretty pleased that I could apply as much as I could.
| Challenge | Category | Value |
|---|---|---|
| Robots. Yeah, I know, pretty obvious. | Web | 25 |
| Strong Password | Misc | 1 |
| BTS-Crazed | Forensics | 75 |
| HOOOOOOOOOOMEEEEEE RUNNNNNNNNNNNNN!!!!! | Cryptography | 50 |
| No Sleep | Web | 100 |
| Phishing for Flags | Web | 105 |
I liked this CTF for a good number of reasons:
- Unlike some of the prior competitions I’ve been a part of, my intuition led to very deliberate (and occasionally, fruitful) actions. This was a refreshing change of pace from aimlessly and frustratingly grasping at straws.
- I was able to branch out across a variety of problem types and solved several problems that were outside my realm of expertise (namely, the Web ones). Usually, I end up spending a disproportionate amount of time in the General Skills, Forensics/Steganography, and OSINT problems.
- Rather than play alone, I got to hack alongside a friend of mine (who is comparably skilled).
Anyways, let’s check out some solutions:
Robots. Yeah, I know, pretty obvious.
So, we know that Delphine is a cook. A wonderful one, at that. But did you know that GIANt used to make robots? Yeah, GIANt robots.
This challenge implies we work with the robots.txt page. A robots.txt webpage tells search engine crawlers which pages or files the crawler can or can’t request from your site. This is used mainly to avoid overloading your site with requests; while the presence of a robots.txt page in a website does not in itself present a security vulnerability, it is often used to identify restricted/private areas of a site’s contents. With that in mind and no other url to examine, we check the robots.txt page for the CTF domain at:
https://riceteacatpanda.wtf/robots.txt
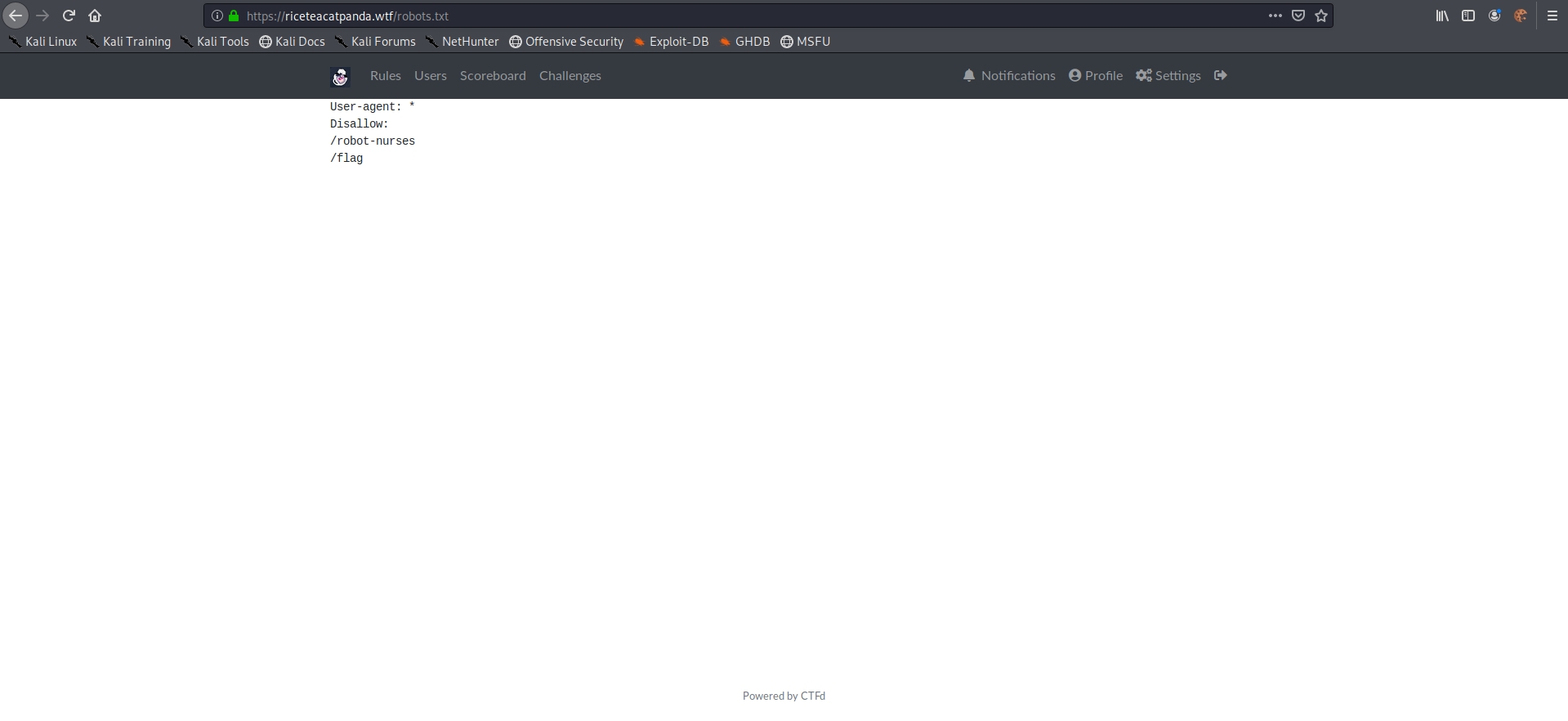
With those results, there are two pages that the robots.txt page reveals to us:
- /robots-nurses
- /flag
The obvious webpage is actually a red-herring. The actual webpage we want is /robots-nurses, which outputs:
rtcp{r0b0t5_4r3_g01ng_t0_t4k3_0v3r_4nd_w3_4r3_s0_scr3w3d}
Strong Password
Eat, Drink, Pet, Hug, Repeat!
flags are entered in the format rtcp{flag}
This challenge is less of a technical one and more of a puzzle. Truthfully, this challenge was meant to be low-hanging fruit in prepping a competitor for the CTF mindset.
Taking a look, the puzzle’s clue appears at a glance to be a nonsensical list of verbs. But upon closer inspection, these verbs correlate to the competition’s name:
| rice | tea | cat | panda |
|---|---|---|---|
| eat | drink | pet | hug |
If we attempt to align that to the flag format we successfully get:
rtcp{rice_tea_cat_panda}
BTS-Crazed
My friend made this cool remix, and it’s pretty good, but everyone says there’s a deeper meaning in the music. To be honest, I can’t really tell - the second drop’s 808s are just too epic.
This is a basic forensics/steganography challenge. Steganography (“stego”) is the practice of obfuscating/concealing messages within other media. In being concealed in such a fashion, the message’s transmission is even concealed. One famous instance in the use of stego was done by Admiral Jeremiah Denton as a P.O.W. in the Vietnam War; in a recorded statement from captivity, Admiral Denton hid a message in his taped statement, blinking the word “TORTURE” via Morse Code.
Fortunately, our challenge is much less dangerous. In our case, we have a .wav audio file with a flag hidden somewhere. One of the first steps you should always take in a challenge like this is to use the strings command in order to see if anything worthwhile is output. Additionally, since we know the flag format, we can grep as a filter:
root@kali:~/Downloads strings 'Save Me.mp3' | grep rtcp
rtcp{j^cks0n_3ats_r1c3}N
And there’s the flag:
rtcp{j^cks0n_3ats_r1c3}
HOOOOOOOOOOMEEEEEE RUNNNNNNNNNNNNN!!!!!
AND JAKE IS ROUNDING THE BASES
HE PASSES BASE 32!!!
HE ROUNDS BASE 64!!!!!!!
WE’RE WITNESSING A MIRACLE!!!!!!!!!!!!!Just one more base to go ;D
Ecbf1HZ_kd8jR5K?[”;(7;aJp?[4>J?Slk3<+n’pF]W^,F>._lB/=r
This challenge hints that we are dealing with encoding schemes (a play on baseball’s “bases” with base32 and base64). However, if you were to decode the message with either of those (or even both), the message remains non-sensical. The clue suggests there may be yet one more enconding scheme for us to consider. One such alternative encoding scheme is Base85 (otherwise known as ASCII85); it uses 5 ASCII characters to represent four bytes of binary data, making it more efficient than Base64.
While there are command-line tools designed for making sense of Base85, we’ll make use of cryptii.org, a phenomenal website for quickly encoding/decoding messages.
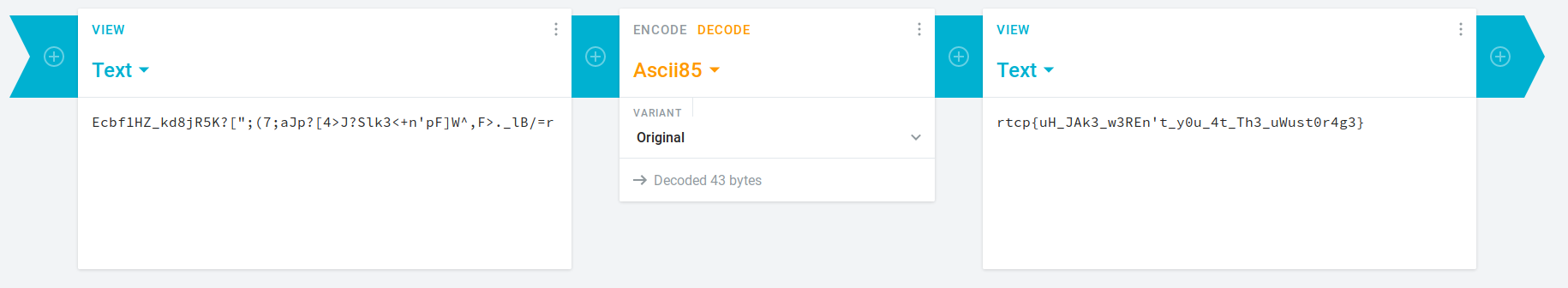
Success! The flag is:
rtcp{uH_JAk3_w3REn’t_y0u_4t_Th3_uWust0r4g3}
No Sleep
Jess doesn’t get enough sleep, since he’s such a gamer so in this challenge, you’ll be staying up with him until 4:00 in the morning :D on a Monday! Let’s go, gamers!
This challenge presents us with a webpage with a countdown clock. While we could wait the amount of time until the page unlocks and reveals to us the flag, there is - naturally - an alternative we could consider.
If we examine the page’s code using our browser’s developer tools (f12 on most keyboards), we can see can the following script within the page’s HTML:
<script>
var _0x1d8e=['gamerfuel=Jan\x2027,\x208020\x2004:20:00',
'Jan\x2027,\x208020\x2004:20:00',
'getTime',
'exec',
'floor',
'getElementById',
'gamer\x20timer',
'AES',
'decrypt',
'U2FsdGVkX18kRm6FDkRVQfVuNPTxyOnJzpu8QnI/9UKoCXp6hQcley11nBnLIItj',
'ok\x20boomer',
'innerHTML',
'Utf8',
'cookie'];
...//elipses added by author to abbreviate code
</script>
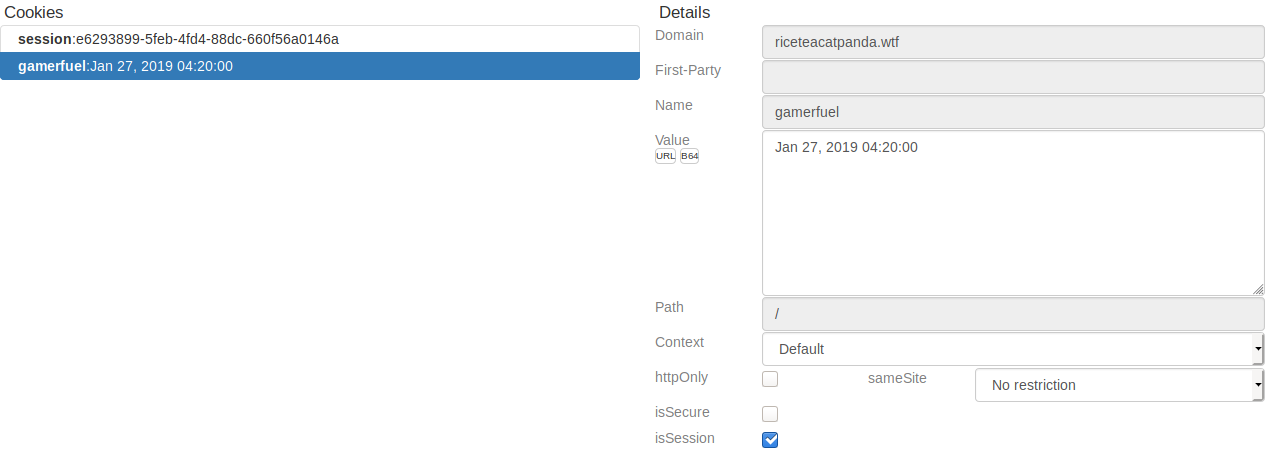
Interestingly, we observe that the webpage appears to be waiting for the client to connect after a particular date. If we observe our cookies, we can likewise see the present date stored inside. This suggests that we are meant to exploit the webpage by manipulating cookies.
Cookies are used by the variety of agents that provide services across the internet as a commercial technique for understanding users and their needs. Cookies are normally data that a web site stores to a user’s computer as a text file whenever the user visits the web site. Cookies include records about performed actions or preferences that are set during the user’s visit on the web site. Whenever the user returns to the same web site, the web site reads the stored cookie to display appropriate contents.
In this challenge, we’ll be using a Firefox extension called Cookie Quick Manager to manipulate our browser’s cookies. If we open the extension and search for cookies related to the RiceTeaCatPanda domain, we quickly see:
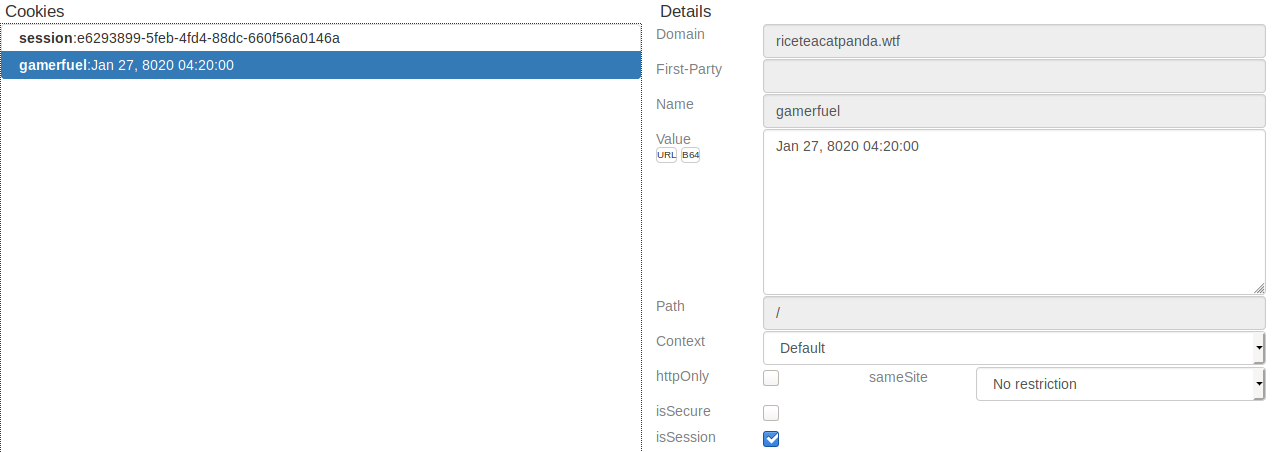
Let’s alter the cookie to a date that has already passed and save the cookie:
This will automatically update our session with the webpage, giving us the flag:
rtcp{w0w_d1d_u_st4y_up?}
Phishing For Flags
I got a bunch of emails from people across the galaxy… some are more interesting than others.
(Zip folder used for the challenge)
This challenge encourages us to excercise a keen eye to look out for phishing messages. In extracting the zip folder, we can see a series of emails:
root@kali:~/Downloads# cd Emails/
root@kali:~/Downloads/Emails# ls
'Applying For A Job.eml'
'College of Flag.eml'
'CONFIRM YOUR UNSUBSCIBE REQUEST.eml'
'GIVE ME BACK MY EYEHOLES.eml'
'Please Verify Your Account (RiceTeaCatPanda).eml'
'Updates on my reseach.eml'
Of all of the email subject lines we might expect to see in a typical inbox, the most likely candidate to be suspicious is probably ‘GIVE ME BACK MY EYEHOLES.eml’. We cat the email file and observe:
root@kali:~/Downloads/Emails# cat 'GIVE ME BACK MY EYEHOLES.eml'
MIME-Version: 1.0
Date: Mon, 18 Nov 2019 10:31:11 -0800
Message-ID: <CAHbBcduwrSDvJ2DWCg8XiH31+rkoLgEEQuEpxG-2=vMsjd0uyA@mail.gmail.com>
Subject: GIVE ME BACK MY EYEHOLES
From: Eyehole Man <eyeholeman@holez.org>
To: Jerry Smith <jerrysmith@james.com>
Content-Type: multipart/alternative; boundary="000000000000f5b3a00597a3260d"
--000000000000f5b3a00597a3260d
Content-Type: text/plain; charset="UTF-8"
I'm the eyeho-hole man! I'm the only one who's allowed to have eyeholes!
Get up on out of here with my Eyeholes!
GIVE ME BACK M-MY EYEHOLES
<https://riceteacatpanda.wtf/phishingemail>
--000000000000f5b3a00597a3260d
Content-Type: text/html; charset="UTF-8"
Content-Transfer-Encoding: quoted-printable
<div dir=3D"ltr"><div>I'm the eyeho-hole man! I'm the only one who&=
#39;s allowed to have eyeholes!=C2=A0<br></div><div><br></div><div>Get up o=
n out of here with my Eyeholes!<br></div><div><br></div><div>GIVE ME BACK M=
-MY <a href=3D"https://riceteacatpanda.wtf/phishingemail">EYEHOLES</a></div=
></div>
--000000000000f5b3a00597a3260d--
Humorous text aside, the most interesting part of this email appears to be a webpage that is similar to the domain that the challenges are hosted on:
https://riceteacatpanda.wtf/phishingemail
Navigating to it reveals the flag:
rtcp{r34d_b3f0rE_yOU_C1iCk}
Afterthoughts
There were a series of challenges that I learned I was on the right-track to solving, particularly:
- “BASmati ricE 64”: I received the appropriate string, but failed to recognize it as being base64 encoded.
- “Uwu?”: I recognized I needed to use burpsuite to intercept proxxied messages to/from the server, but didn’t identify the page with the flag.
- “15”: I correctly identified that the message was using a letter substitution cipher, but could not determine what the cipher was.
I was frustrated I couldn’t get much traction with the reverse engineering or binary problems. I’m hoping that after this semester’s course on Assembly Language and some dedicated online resources, I’ll be able to understand and perform better on them.
Other than that, this was a wonderful CTF and I had a brilliant time being a part of it.
Finally, attribution for art used in this post:
Icons made by Freepik from www.flaticon.com.